How Do I Know If My iPhone Is Synced to Another Device?

With our lives increasingly intertwined with the digital world, the security and privacy of our mobile devices have never been more critical. Despite the fact that iPhones are known for their robust security features, no device is completely immune to unauthorized access and synchronization issues. Let's check out how to identify if your iPhone is synced to another device, recognize signs of unauthorized access, and ensure your digital safety.
Understanding iPhone Synchronization
What Does iPhone Synchronization Mean?
Synchronization allows your iPhone to share and update information across other devices using the same Apple ID. This feature is designed to make your digital life more seamless, ensuring access to your contacts, emails, photos, and more, across all your devices.
How to Tell If Your iPhone Is Synced to Another Phone
1. Check Your Apple ID Devices List:
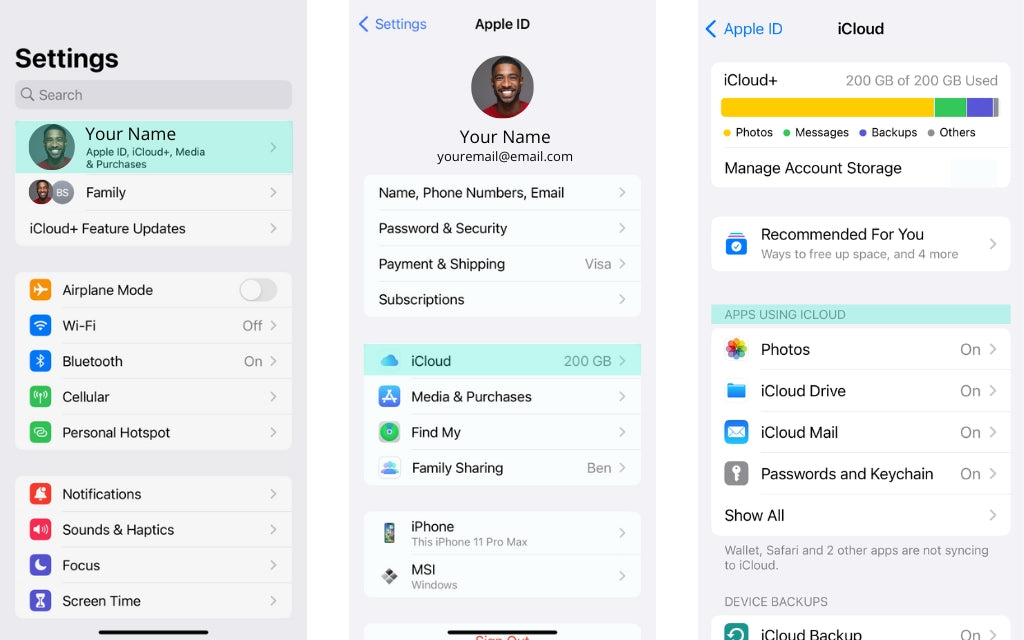
- Go to Settings and tap on your name at the top.
- Scroll to find the "Devices" section. Here, you'll see a list of devices that are currently using or have access to your Apple ID and iCloud. If you see any device you don't recognize or no longer use, you can remove it from this list.
2. Look for Synced Data Across Devices:
- Observe if data like contacts, messages, photos, and notes appear on another device that you didn't manually put there. This could indicate that both devices are using the same Apple ID.
- For example, if new contacts added to your iPhone automatically appear on another device, it's a sign they're synced.
3. Use the Find My App:
- The Find My app shows the location of devices where you're signed in with the same Apple ID.
- Open the Find My app, and if you see another iPhone’s location being displayed alongside your device, it’s likely synced with your Apple ID.
4. Check for Unexpected Apple ID Sign-In Notifications:
- Apple sends notifications and emails when your Apple ID is used to sign in to a new device.
- If you receive a notification about a sign-in you don't recognize, it could indicate that someone else has access to your Apple ID and is syncing their device with yours.
5. Review Messages and FaceTime:
- If messages or FaceTime calls intended for you are being received on another device, this is a strong indicator that your devices are synced. Check the settings in both Messages and FaceTime to see which devices are enabled to receive calls and messages.
6. iCloud Photo Library and Shared Albums:
- Check your Photos app for unexpected shared albums or photos that you didn’t take. If your iCloud Photo Library is synced across devices with the same Apple ID, photos taken from one device will appear on all devices connected to that iCloud account.
Steps to Unsync or Secure Your Device
If you find that your iPhone is undesirably synced with another phone, you can take the following steps to secure your device:
- Change Your Apple ID Password: Immediately change your Apple ID password to prevent unauthorized access.
- Sign Out of Unrecognized Devices: Go to the Apple ID Devices list (as described above) and remove any device you do not recognize or no longer use.
- Enable Two-Factor Authentication: This adds an extra layer of security by requiring a verification code, in addition to your password, whenever you sign in to a new device.
- Review and Adjust Sharing Settings: In your iCloud, Messages, and FaceTime settings, review and adjust which devices can receive and send messages or calls.
How to Check Synchronization With iCloud
- iCloud Settings: Go to Settings > [your name] > iCloud. Here, you can see which types of data are being synced (like Contacts, Calendars, Photos, etc.).
- iTunes & Finder: Check for synchronization with computers through iTunes (for older macOS versions or PCs) or Finder (for macOS Catalina and later).
Can Someone Access My iPhone from Another Device?
Understanding Remote Access
Remote access to an iPhone can occur in a few ways:
- iCloud Access: Someone with your Apple ID credentials can access information stored in iCloud.
- Third-Party Apps: Applications that enable remote control or monitoring could potentially provide access to your device.
Preventing Unauthorized Access
- Secure Your Apple ID: Use a strong, unique password and enable two-factor authentication.
-
Be Cautious with Third-Party Apps: Only download apps from trusted sources and review the permissions they request.
Can someone mirror your phone without your permission?
technically possible for someone to mirror your phone without your permission, though it typically requires some level of access to your device or its credentials. Phone mirroring involves displaying the contents of one device onto another screen in real-time. This can be used legitimately for sharing presentations, teaching, or troubleshooting purposes. However, it can also be exploited for unauthorized surveillance or data theft. Here's how unauthorized mirroring might occur:
- Using Spyware or Malware: Malicious software can be installed on a victim's phone without their knowledge, often disguised as a legitimate app. Once installed, the software can enable an attacker to mirror the victim's phone screen and control it remotely.
- Misuse of Legitimate Apps: Some legitimate remote access and monitoring apps can be misused for mirroring a phone without consent. If someone gains physical access to your device, they could install such an app and monitor your activities remotely.
- Exploiting Security Vulnerabilities: Attackers might exploit security vulnerabilities in the phone’s operating system or in connected services to gain unauthorized access and mirror the device's screen.
- Phishing Attacks: Phishing or social engineering attacks can trick users into granting access to their devices or sharing sensitive information like passwords, making it easier for attackers to install mirroring software.
Preventing Unauthorized Mirroring
Use Strong Passwords and Enable Two-Factor Authentication: Protect your accounts and devices with strong, unique passwords and, where available, enable two-factor authentication to add an extra layer of security.Install Security Software: Use reputable security software on your smartphone to detect and block malware or spyware.Regularly Update Your Devices: Keep your operating system and all apps up to date to protect against known vulnerabilities.Be Cautious with App Permissions: Only download apps from trusted sources like the Apple App Store or Google Play Store, and carefully review the permissions each app requests. Be wary of granting extensive permissions without a clear need.Educate Yourself on Phishing Scams: Be aware of common phishing tactics and never click on suspicious links or attachments, especially from unknown sources.Physical Security: Keep your device secure and never leave it unattended in public places. Use features like biometric locks and auto-lock to prevent unauthorized access if your phone is lost or stolen.
While it's challenging to guarantee 100% security, taking these precautions can significantly reduce the risk of unauthorized phone mirroring and help protect your personal information and privacy.
Signs Your iPhone May Be Connected to Another Device
Unexpected Behavior
- Battery Draining Quickly: Unusual battery drain can indicate background processes related to syncing or malicious activity.
- Unfamiliar Apps: The presence of apps you don't remember downloading could be a sign of unauthorized access.
- Increased Data Usage: A significant increase in data usage might suggest your information is being synced or transmitted without your knowledge.
How to Investigate
- Review Installed Apps: Regularly check your apps and delete any that you don't recognize or use.
- Check Device Locations: In Settings > [your name] > Find My, you can see the location of your devices. An unfamiliar location may indicate someone else has access.
Enhancing Your iPhone's Security
Regular Updates
Keeping your iOS and apps up to date is crucial for security. Updates often include patches for vulnerabilities that could be exploited by attackers.
Privacy Settings
- App Permissions: Regularly review the permissions granted to each app and adjust them according to your needs.
- Location Services: Be mindful of which apps have access to your location and limit this access when not necessary.
Being Vigilant
- Phishing Attempts: Be wary of suspicious emails or messages asking for your personal information or directing you to log in to your Apple ID.
- Public Wi-Fi Networks: Use secure networks or a VPN to protect your data when connected to public Wi-Fi.
In an era where digital privacy is constantly under threat, being informed and vigilant is your best defense. By understanding how synchronization works, recognizing the signs of unauthorized access, and taking steps to enhance your iPhone's security, you can protect your digital life. Regularly reviewing your device's connections and settings ensures you stay one step ahead of potential security risks.